Gtc Blackboard Authentication Failed Try Again
This page provides a full general overview of the Security Exclamation Markup Language (SAML) 2.0 Building Block forth with mutual Unmarried Sign-On (SSO) issues and troubleshooting techniques for the SAML authentication provider.
If for whatever reason an updated/new IdP metadata XML file is uploaded in the Blackboard Acquire GUI on the SAML Authentication Settings page in the Identity Provider Settings section for a SAML authentication provider, the SAML B2 and that SAML authentication provider should as well exist toggled Inactive/Available, while having the SAML authentication provider in 'Agile' status, to ensure any buried IdP metadata is cleared out and the updated IdP metadata is fully utilized.
Key terms
The post-obit terms and abbreviations are used throughout this guide:
- SAML: Security Assertion Markup Language
- IdP: Identity Provider
- SP: Service Provider
- ADFS: Agile Directory Federation Services
- GUI: Graphical User Interface. In the context of Blackboard Learn, this means working within the software.
Edit SAML configuration settings
To assistance troubleshoot SAML hallmark issues, the SAML Building Block was updated in release 3200.2.0 to include these configuration settings and options:
- Define the SAML session age limit
- Choose a signature algorithm type
- Regenerate certificates
- Alter the ResponseSkew value
More than on how to configure settings in the SAML Building Cake
Errors and exceptions
SAML related errors/exceptions are captured in the following logs:
- /usr/local/blackboard/logs/bb-services-log.txt
- /usr/local/blackboard/logs/tomcat/stdout-stderr-<appointment>.log
- /usr/local/blackboard/logs/tomcat/catalina-log.txt
These logs should always be searched when investigating a reported SAML authentication issue.
SAML Tracer
With SAML 2.0 authentication troubleshooting iterations, at some betoken it may be necessary to confirm/view the attributes that are actually being released from the IdP and sent to Learn during the authentication process. If the attributes from the IdP are NOT encrypted in the SAML response, the Firefox browser SAML tracer Improver or Chrome SAML Message Decoder can exist used to view the attributes.
Attribute not properly mapped
If the aspect containing the userName is not properly mapped as specified in the Remote User ID field in the Map SAML Attributes department on the SAML Authentication Settings folio in the Blackboard Learn GUI, the following upshot will be logged in the bb-services log when attempting to login to Blackboard Acquire via SAML authentication:
2016-06-28 12:48:12 -0400 - userName is null or empty
A like Sign On Error! message displayed in the browser: Blackboard Learn is currently unable to log into your account using unmarried-sign on. Contact your ambassador for aid.
An Authentication Failure entry appears in the bb-services log:
2016-06-28 12:48:12 -0400 - BbSAMLExceptionHandleFilter - javax.servlet.ServletException: Authentication Failure
at blackboard.auth.provider.saml.customization.handler.BbAuthenticationSuccessHandler.checkAuthenticationResult(BbAuthenticationSuccessHandler.java:81)
at blackboard.auth.provider.saml.customization.handler.BbAuthenticationSuccessHandler.onAuthenticationSuccess(BbAuthenticationSuccessHandler.java:57)
at org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter.successfulAuthentication(AbstractAuthenticationProcessingFilter.java:331)
at org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.coffee:245)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.coffee:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64) at org.springframework.spider web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53) at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.coffee:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.coffee:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.coffee:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.coffee:262)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sunday.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.coffee:62)
at sun.reverberate.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:497)
[SNIP]
Resolution
You take ii options to resolve the issue. Offset, select the Create accounts if they don't exist in the system option on the SAML Authentication Settings page in the Blackboard Learn GUI. Alternatively, you tin can attempt to view the value of the attributes released past the IdP via SAML tracer or Debug Logging if the attributes are NOT encrypted:
<saml2:Attribute Proper name="urn:oid:0.9.2342.19200300.100.ane.iii">
<saml2:AttributeValue xmlns:xs="http://www.w3.org/2001/XMLSchema"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-example"
xsi:type="xs:anyType"
>bbuser_saml2@bbchjones.net</saml2:AttributeValue>
</saml2:Aspect>
and map the Attribute Name that has the desired AttributeValue to the Remote User ID on the SAML Authentication Settings page in the Blackboard Acquire GUI.
Compatible information source non selected
Users won't be able to login to Blackboard Learn via SAML authentication if the Data Source for the users is not selected in the Services Provider Settings > Uniform Data Sources section on the SAML Authentication Settings page in the Blackboard Learn GUI. The following event volition exist logged in the bb-services log when attempting to log in to Blackboard Learn via SAML authentication:
2016-09-23 12:33:13 -0500 - userName is null or empty
The Sign On Error! bulletin appears in the browser, as well as the Authentication Failure in the bb-services log:
2016-09-23 12:33:thirteen -0500 - BbSAMLExceptionHandleFilter - javax.servlet.ServletException: Hallmark Failure
at blackboard.auth.provider.saml.customization.handler.BbAuthenticationSuccessHandler.checkAuthenticationResult(BbAuthenticationSuccessHandler.coffee:82)
at blackboard.auth.provider.saml.customization.handler.BbAuthenticationSuccessHandler.onAuthenticationSuccess(BbAuthenticationSuccessHandler.java:58)
at org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter.successfulAuthentication(AbstractAuthenticationProcessingFilter.java:331)
at org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.coffee:245)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.coffee:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.coffee:64)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.coffee:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.SecurityContextPersistenceFilter.doFilter (SecurityContextPersistenceFilter.coffee:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:176)
at org.springframework.spider web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:262)
at sun.reverberate.GeneratedMethodAccessor3399.invoke(Unknown Source)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at coffee.lang.reflect.Method.invoke(Method.java:498)
[SNIP]
Resolution
- Obtain the username of a user that is unable to login.
- In the Blackboard Learn GUI, navigate to Organization Admin > Users and search for the user.
- Copy the Data Source Cardinal of the user.
- Navigate to System Admin > Authentication > "Provider Name" > SAML Settings > Compatible Information Sources.
- Place a bank check mark side by side to that Data Source in the Proper noun column and select Submit.
"Given URL is not well formed" error bulletin
If OneLogin is configured equally the IdP for the SAML hallmark provider in Blackboard Learn, a Given URL is not well formed error may be displayed on the page after inbound the OneLogin credentials when attempting login to Blackboard Learn.
With the following displayed in the bb-services-log:
2016-09-16 09:43:40 -0400 - Given URL is non well formed<P><bridge class="captionText">For reference, the Error ID is 17500f44-7809-4b9f-a272-3bed1d1af131.</span> - java.lang.IllegalArgumentException: Given URL is not well formed
at org.opensaml.util.URLBuilder.<init>(URLBuilder.java:120)
at org.opensaml.util.SimpleURLCanonicalizer.canonicalize(SimpleURLCanonicalizer.java:87)
at org.opensaml.common.bounden.decoding.BasicURLComparator.compare(BasicURLComparator.java:57)
at org.opensaml.common.binding.decoding.BaseSAMLMessageDecoder.compareEndpointURIs(BaseSAMLMessageDecoder.java:173)
at org.opensaml.mutual.binding.decoding.BaseSAMLMessageDecoder.checkEndpointURI(BaseSAMLMessageDecoder.java:213)
at org.opensaml.saml2.binding.decoding.BaseSAML2MessageDecoder.decode(BaseSAML2MessageDecoder.coffee:72)
at org.springframework.security.saml.processor.SAMLProcessorImpl.retrieveMessage(SAMLProcessorImpl.java:105)
at org.springframework.security.saml.processor.SAMLProcessorImpl.retrieveMessage(SAMLProcessorImpl.java:172)
at org.springframework.security.saml.SAMLProcessingFilter.attemptAuthentication(SAMLProcessingFilter.java:80)
at org.springframework.security.spider web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.java:217)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.coffee:213)
at org.springframework.security.spider web.FilterChainProxy.doFilter(FilterChainProxy.java:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
[SNIP]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:617)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.java:745)
Acquired by: coffee.net.MalformedURLException: no protocol: {recipient}
at java.cyberspace.URL.<init>(URL.java:593)
at java.net.URL.<init>(URL.java:490)
at java.internet.URL.<init>(URL.java:439)
at org.opensaml.util.URLBuilder.<init>(URLBuilder.java:77)
... 203 more
Resolution
- Plow on the Firefox browser SAML tracer and replicate the login event.
- Review the beginning of the SAML Postal service event:
<samlp:Response Destination="{recipient}"
ID="R8afbfbfee7292613f98ad4ec4115de7c6b385be6"
InResponseTo="a3g2424154bb0gjh3737ii66dadbff4"
IssueInstant="2016-09-16T18:49:09Z"
Version="2.0"
xmlns:saml="urn:oasis:names:tc:SAML:2.0:assertion"
xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"
>
<saml:Issuer>https://app.onelogin.com/saml/metadata/123456</saml:Issuer>
[SNIP] - For line 1 with the Response, find that the Destination= is merely set to recipient.
- Take the client access the Configuration section of their OneLogin IdP.
- Confirm if the Recipient field is blank.
- Re-create the value of the ACS (Consumer) URL, paste it into the Recipient field and select Relieve.
IdP/SP Trouble Scenarios
- If an error appears before y'all are redirected to the IdP's login page, the IdP's metadata may be invalid.
- If an error appears after yous log in on the IdP'due south page, the reasons could exist that:
- Attribute mapping between the SP and IdP is incorrect, or the IdP didn't return a valid Remote User ID.
- The SAML response from the IdP wasn't validated by the SP. This could exist acquired by:
- The IdP signs the SAML response with a certificate that is not issued by a valid document authority, and the SP's keystore doesn't incorporate this certificate.
- The SP's system clock is incorrect.
Active Directory Federation Services (ADFS)
The attribute names are case sensitive in the Map SAML Attributes section on the SAML Authentication Settings page in the Blackboard Learn GUI. So if the Remote User ID has sAMAccountName for the Attribute Name on the settings folio and the actual SAML POST from the IdP has this for the Attribute Name in the AttributeStatement:
<AttributeStatement>
<Attribute Name="SamAccountName>
<AttributeValue>Test-User</AttributeValue>
</Aspect>
</AttributeStatement>
The user volition not exist able to login. The Remote User ID attribute name value on the SAML Hallmark Settings page would need to be changed from sAMAccountName to SamAccountName.
"Resource non constitute" or "Sign on mistake!" warning
This department contains some of the common problems that may prevent a user from logging into Learn via SAML hallmark with ADFS when The specified resource was not plant, or you exercise not take permission to access it or Sign On Error! message is displayed in the Blackboard Learn GUI.
Problem #1
After entering the login credentials on the ADFS login page, an fault may be displayed after being redirected to the Blackboard Learn GUI: The specified resource was not found, or you practise non take permission to access information technology.
With a corresponding message in the stdout-stderr log:
INFO | jvm ane | 2016/06/22 06:08:33 | - No mapping plant for HTTP request with URI [/auth-saml/saml/SSO] in DispatcherServlet with name 'saml'
The problem occurs because the noHandlerFound() method is used in the DispatcherServlet.java lawmaking and is unable to locate/map the HTTP SSO asking.
/**
* No handler found -> set appropriate HTTP response status.
* @param asking current HTTP request
* @param response electric current HTTP response
* @throws Exception if preparing the response failed
*/
protected void noHandlerFound(HttpServletRequest request, HttpServletResponse response) throws Exception {
if (pageNotFoundLogger.isWarnEnabled()) {
pageNotFoundLogger.warn("No mapping plant for HTTP request with URI [" + getRequestUri(request) +
"] in DispatcherServlet with name '" + getServletName() + "'");
}
if (this.throwExceptionIfNoHandlerFound) {
throw new NoHandlerFoundException(asking.getMethod(), getRequestUri(request),
new ServletServerHttpRequest(request).getHeaders());
}
else {
response.sendError(HttpServletResponse.SC_NOT_FOUND);
}
}
Resolution
This typically occurs considering the Entity ID for the SP configured in the Blackboard Learn GUI is incorrect. This can be resolved by navigating to System Admin > Authentication > SAML Authentication Settings > Service Provider Settings and updating the Entity ID. For ADFS, the default configuration for the Entity ID would be https://[Learn Server Hostname]/auth-saml/saml/SSO.
If a school changes their URL from the default https://school.blackboard.com to https://their.school.edu, the Entity ID in the Blackboard Larn GUI on the SAML Authentication Settings page should be updated to https://their.school.edu/auth-saml/saml/SSO.
Problem #two
Subsequently entering the login credentials on the ADFS login page, an error may be displayed later being redirected to the Blackboard Learn GUI: The specified resource was not found, or you do not have permission to access it.
With this respective bulletin in the stdout-stderr log:
INFO | jvm i | 2016/06/22 06:08:33 | - No mapping found for HTTP request with URI [/auth-saml/saml/SSO] in DispatcherServlet with name 'saml'
And this message in the catalina log:
Mistake 2016-06-27 10:47:03,664 connector-half dozen: userId=_2_1, sessionId=62536416FB80462298C92064A7022E50 org.opensaml.xml.encryption.Decrypter - Error decrypting the encrypted data element
org.apache.xml.security.encryption.XMLEncryptionException: Illegal central size
Original Exception was java.security.InvalidKeyException: Illegal key size
at org.apache.xml.security.encryption.XMLCipher.decryptToByteArray(XMLCipher.java:1822)
at org.opensaml.xml.encryption.Decrypter.decryptDataToDOM(Decrypter.java:596)
at org.opensaml.xml.encryption.Decrypter.decryptUsingResolvedEncryptedKey(Decrypter.java:795)
at org.opensaml.xml.encryption.Decrypter.decryptDataToDOM(Decrypter.java:535)
at org.opensaml.xml.encryption.Decrypter.decryptDataToList(Decrypter.coffee:453)
at org.opensaml.xml.encryption.Decrypter.decryptData(Decrypter.java:414)
at org.opensaml.saml2.encryption.Decrypter.decryptData(Decrypter.coffee:141)
at org.opensaml.saml2.encryption.Decrypter.decrypt(Decrypter.java:69)
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.java:199)
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:82)
at org.springframework.security.hallmark.ProviderManager.cosign(ProviderManager.coffee:167)
[SNIP]
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.java:745)
Caused by: java.security.InvalidKeyException: Illegal key size
at javax.crypto.Nix.checkCryptoPerm(Cipher.coffee:1039)
at javax.crypto.Cypher.init(Nix.java:1393)
at javax.crypto.Zip.init(Cipher.java:1327)
at org.apache.xml.security.encryption.XMLCipher.decryptToByteArray(XMLCipher.coffee:1820)
... 205 more
And this message displayed in the bb-services log:
2016-06-27 10:47:03 -0400 - unsuccessfulAuthentication - org.springframework.security.authentication.AuthenticationServiceException: Error validating SAML bulletin
at org.springframework.security.saml.SAMLAuthenticationProvider.cosign(SAMLAuthenticationProvider.java:100)
at org.springframework.security.hallmark.ProviderManager.authenticate(ProviderManager.java:167)
at org.springframework.security.saml.SAMLProcessingFilter.attemptAuthentication(SAMLProcessingFilter.java:87)
at org.springframework.security.web.hallmark.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.coffee:217)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53)
at org.springframework.spider web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:262)
at sun.reflect.GeneratedMethodAccessor3422.invoke(Unknown Source)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.coffee:43)
at coffee.lang.reflect.Method.invoke(Method.java:498)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.java:277)
at org.apache.catalina.security.SecurityUtil$i.run(SecurityUtil.java:274)
at coffee.security.AccessController.doPrivileged(Native Method)
at javax.security.auth.Bailiwick.doAsPrivileged(Subject.coffee:549)
at org.apache.catalina.security.SecurityUtil.execute(SecurityUtil.java:309)
at org.apache.catalina.security.SecurityUtil.doAsPrivilege(SecurityUtil.coffee:249)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:237)
at org.apache.catalina.cadre.ApplicationFilterChain.access$000(ApplicationFilterChain.java:55)
at org.apache.catalina.core.ApplicationFilterChain$1.run(ApplicationFilterChain.java:191)
at org.apache.catalina.core.ApplicationFilterChain$i.run(ApplicationFilterChain.java:187)
at java.security.AccessController.doPrivileged(Native Method)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.coffee:186)
at blackboard.auth.provider.saml.customization.filter.BbSAMLExceptionHandleFilter.doFilterInternal(BbSAMLExceptionHandleFilter.java:thirty)
at org.springframework.spider web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at sun.reflect.GeneratedMethodAccessor3421.invoke(Unknown Source)
[SNIP]
at coffee.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.coffee:617)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.java:745)
Acquired by: org.opensaml.common.SAMLException: Response doesn't have any valid assertion which would laissez passer subject validation
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.coffee:229)
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:87)
... 229 more
The trouble occurs because past default ADFS encrypts the attributes it sends using AES-256 and the Java runtime used by Blackboard Learn doesn't support AES-256 out of the box.
Resolution
A universal resolution selection is to open a PowerShell on the ADFS server and set the relying party created for Blackboard Learn to transport the attributes as unencrypted. As the whole communication is over SSL, this volition not reduce the security of the hallmark. It also makes debugging of whatsoever issues easier as the attributes can exist viewed using debugging tools such every bit the Firefox browser SAML tracer Addition and a restart of the Blackboard Learn organisation is not required. To ready the relying party created for Blackboard Learn to transport the attributes as unencrypted, open a PowerShell and execute the following control, replacing TargetName with the name of the Relying Party Trust that is in the ADFS Management Console under Trust Relationships > Relying Party Trusts.
set-ADFSRelyingPartyTrust –TargetName "yourlearnserver.blackboard.com" –EncryptClaims $False
After this change the ADFS service volition demand to be restarted with the command: Restart-Service ADFSSRV
Trouble #3
After entering the login credentials on the ADFS login page, an error may be displayed after being redirected to the Blackboard Learn GUI: The specified resource was non found, or you do not have permission to access information technology or Sign On Error!
With either, these similar corresponding SAML related events appear in the stdout-stderr log:
INFO | jvm 1 | 2016/09/06 xx:33:04 | - /saml/login?apId=_107_1&redirectUrl=https%3A%2F%2Fbb.fraser.misd.net%2Fwebapps%2Fportal%2Fexecute%2FdefaultTab at position i of ten in additional filter chain; firing Filter: 'SecurityContextPersistenceFilter'
INFO | jvm 1 | 2016/09/06 20:33:04 | - No HttpSession currently exists
INFO | jvm i | 2016/09/06 20:33:04 | - No SecurityContext was bachelor from the HttpSession: null. A new i volition exist created.
INFO | jvm 1 | 2016/09/06 20:33:04 | - /saml/login?apId=_107_1&redirectUrl=https%3A%2F%2Fbb.fraser.misd.cyberspace%2Fwebapps%2Fportal%2Fexecute%2FdefaultTab at position ii of ten in additional filter chain; firing Filter: 'WebAsyncManagerIntegrationFilter'
INFO | jvm one | 2016/09/06 20:33:04 | - /saml/login?apId=_107_1&redirectUrl=https%3A%2F%2Fbb.fraser.misd.net%2Fwebapps%2Fportal%2Fexecute%2FdefaultTab at position 3 of 10 in boosted filter concatenation; firing Filter: 'HeaderWriterFilter'
INFO | jvm 1 | 2016/09/06 20:33:04 | - /saml/login?apId=_107_1&redirectUrl=https%3A%2F%2Fbb.fraser.misd.internet%2Fwebapps%2Fportal%2Fexecute%2FdefaultTab at position 4 of 10 in boosted filter chain; firing Filter: 'FilterChainProxy'
INFO | jvm 1 | 2016/09/06 20:33:04 | - Checking match of request : '/saml/login'; against '/saml/login/**'
INFO | jvm 1 | 2016/09/06 20:33:04 | - /saml/login?apId=_107_1&redirectUrl=https%3A%2F%2Fbb.fraser.misd.net%2Fwebapps%2Fportal%2Fexecute%2FdefaultTab at position one of i in boosted filter chain; firing Filter: 'SAMLEntryPoint'
INFO | jvm 1 | 2016/09/06 20:33:04 | - Asking for URI http://www.w3.org/2000/09/xmldsig#rsa-sha1
INFO | jvm 1 | 2016/09/06 20:33:04 | - Request for URI http://www.w3.org/2000/09/xmldsig#rsa-sha1
INFO | jvm 1 | 2016/09/06 20:33:04 | - SecurityContext is empty or contents are bearding - context volition not be stored in HttpSession.
INFO | jvm i | 2016/09/06 xx:33:04 | - SecurityContextHolder now cleared, as request processing completed
INFO | jvm 1 | 2016/09/06 twenty:33:07 | - /saml/SSO at position one of ten in additional filter chain; firing Filter: 'SecurityContextPersistenceFilter'
INFO | jvm ane | 2016/09/06 20:33:07 | - HttpSession returned cypher object for SPRING_SECURITY_CONTEXT
INFO | jvm 1 | 2016/09/06 twenty:33:07 | - No SecurityContext was available from the HttpSession: [email protected] A new one will exist created.
INFO | jvm i | 2016/09/06 20:33:07 | - /saml/SSO at position two of 10 in additional filter concatenation; firing Filter: 'WebAsyncManagerIntegrationFilter'
INFO | jvm 1 | 2016/09/06 xx:33:07 | - /saml/SSO at position three of 10 in boosted filter concatenation; firing Filter: 'HeaderWriterFilter'
INFO | jvm ane | 2016/09/06 twenty:33:07 | - /saml/SSO at position 4 of x in additional filter chain; firing Filter: 'FilterChainProxy'
INFO | jvm i | 2016/09/06 20:33:07 | - Checking lucifer of request : '/saml/sso'; against '/saml/login/**'
INFO | jvm one | 2016/09/06 20:33:07 | - Checking match of request : '/saml/sso'; against '/saml/logout/**'
INFO | jvm 1 | 2016/09/06 20:33:07 | - Checking lucifer of request : '/saml/sso'; against '/saml/bbsamllogout/**'
INFO | jvm ane | 2016/09/06 twenty:33:07 | - Checking lucifer of request : '/saml/sso'; against '/saml/sso/**'
INFO | jvm 1 | 2016/09/06 twenty:33:07 | - /saml/SSO at position 1 of 1 in additional filter chain; firing Filter: 'SAMLProcessingFilter'
INFO | jvm one | 2016/09/06 twenty:33:07 | - Authentication try using org.springframework.security.saml.SAMLAuthenticationProvider
INFO | jvm 1 | 2016/09/06 xx:33:07 | - Forwarding to /
INFO | jvm 1 | 2016/09/06 20:33:07 | - DispatcherServlet with name 'saml' processing POST asking for [/auth-saml/saml/SSO]
INFO | jvm i | 2016/09/06 xx:33:07 | - No mapping found for HTTP request with URI [/auth-saml/saml/SSO] in DispatcherServlet with proper noun 'saml'
INFO | jvm ane | 2016/09/06 xx:33:07 | - SecurityContext is empty or contents are anonymous - context volition not be stored in HttpSession.
INFO | jvm 1 | 2016/09/06 20:33:07 | - Successfully completed request
INFO | jvm 1 | 2016/09/06 xx:33:07 | - Skip invoking on
INFO | jvm 1 | 2016/09/06 20:33:07 | - SecurityContextHolder at present cleared, as request processing completed
Or these like SAML exceptions in the bb-services log:
2016-11-29 09:04:24 -0500 - unsuccessfulAuthentication - org.springframework.security.authentication.AuthenticationServiceException: Error validating SAML bulletin
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:100)
at org.springframework.security.hallmark.ProviderManager.authenticate(ProviderManager.coffee:167)
at org.springframework.security.saml.SAMLProcessingFilter.attemptAuthentication(SAMLProcessingFilter.java:87)
at org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.coffee:217)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.spider web.FilterChainProxy.doFilter(FilterChainProxy.java:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
at org.springframework.spider web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.coffee:213)
at org.springframework.security.spider web.FilterChainProxy.doFilter(FilterChainProxy.java:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.coffee:262)
at lord's day.reflect.GeneratedMethodAccessor853.invoke(Unknown Source)
at dominicus.reverberate.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.java:282)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.coffee:279)
at java.security.AccessController.doPrivileged(Native Method)
at javax.security.auth.Field of study.doAsPrivileged(Subject.coffee:549)
at org.apache.catalina.security.SecurityUtil.execute(SecurityUtil.java:314)
at org.apache.catalina.security.SecurityUtil.doAsPrivilege(SecurityUtil.java:253)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:190)
at org.apache.catalina.core.ApplicationFilterChain.admission$000(ApplicationFilterChain.coffee:46)
at org.apache.catalina.cadre.ApplicationFilterChain$i.run(ApplicationFilterChain.java:148)
at org.apache.catalina.core.ApplicationFilterChain$1.run(ApplicationFilterChain.coffee:144)
at java.security.AccessController.doPrivileged(Native Method)
at org.apache.catalina.cadre.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:143)
at blackboard.auth.provider.saml.customization.filter.BbSAMLExceptionHandleFilter.doFilterInternal(BbSAMLExceptionHandleFilter.java:30)
at org.springframework.spider web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at sun.reflect.GeneratedMethodAccessor853.invoke(Unknown Source)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.coffee:43)
[SNIP]
at org.apache.catalina.valves.RemoteIpValve.invoke(RemoteIpValve.java:677)
at blackboard.tomcat.valves.LoggingRemoteIpValve.invoke(LoggingRemoteIpValve.java:44)
at org.apache.catalina.core.StandardEngineValve.invoke(StandardEngineValve.coffee:87)
at org.apache.catalina.connector.CoyoteAdapter.service(CoyoteAdapter.java:349)
at org.apache.coyote.http11.Http11Processor.service(Http11Processor.java:1110)
at org.apache.coyote.AbstractProcessorLight.procedure(AbstractProcessorLight.coffee:66)
at org.apache.coyote.AbstractProtocol$ConnectionHandler.process(AbstractProtocol.java:785)
at org.apache.tomcat.util.net.NioEndpoint$SocketProcessor.doRun(NioEndpoint.java:1425)
at org.apache.tomcat.util.internet.SocketProcessorBase.run(SocketProcessorBase.java:49)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1142)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:617)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at coffee.lang.Thread.run(Thread.java:745)
Caused by: org.opensaml.common.SAMLException: Response issue time is either too sometime or with date in the time to come, skew 60, time 2016-11-29T14:03:16.634Z
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.coffee:126)
at blackboard.auth.provider.saml.customization.consumer.BbSAMLWebSSOProfileConsumerImpl.processAuthenticationResponse(BbSAMLWebSSOProfileConsumerImpl.java:40)
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:87)
... 230 more
The problem occurs when the ADFS server and the Blackboard Learn awarding server have a fourth dimension drift shut to or across the default of sixty seconds.
Resolution
There are ii options to resolve the consequence:
- Manually syncing the clocks of the Blackboard Acquire application servers and the ADFS server. For Blackboard Acquire, the current fourth dimension and time zone of the server can be viewed in a web browser by adding /webapps/portal/healthCheck to the end of a Blackboard Larn URL.
Case: https://mhtest1.blackboard.com//webapps/portal/healthCheck
Hostname: ip-x-145-49-11.ec2.internal
Status: Active - Database connectivity established
Running since: Sat, Dec 3, 2016 - 05:39:xi PM EST
Time of asking: Thu, Dec eight, 2016 - 05:12:43 PM ESTAn institution may use the higher up URL to compare the Blackboard Learn system time zone and clock with that of their ADFS server then adjust those items every bit necessary on the ADFS server and then that they are in-sync with the Blackboard Acquire site.
Problem #4
After entering the login credentials on the ADFS login folio, an error may be displayed after being redirected to the Blackboard Larn GUI: The specified resource was not institute, or you practise non have permission to access it or Sign On Error!
With the following exceptions in the bb-services log:
2016-11-01 12:47:19 -0500 - unsuccessfulAuthentication - org.springframework.security.hallmark.AuthenticationServiceException: Mistake validating SAML message
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:100)
at org.springframework.security.authentication.ProviderManager.authenticate(ProviderManager.java:167)
at org.springframework.security.saml.SAMLProcessingFilter.attemptAuthentication(SAMLProcessingFilter.java:87)
at org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.coffee:217)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.spider web.FilterChainProxy.doFilter(FilterChainProxy.java:184)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.coffee:53)
at org.springframework.spider web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.coffee:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.spider web.FilterChainProxy.doFilter(FilterChainProxy.java:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:262)
at dominicus.reflect.GeneratedMethodAccessor929.invoke(Unknown Source)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.java:282)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.java:279)
at java.security.AccessController.doPrivileged(Native Method)
at javax.security.auth.Field of study.doAsPrivileged(Field of study.java:549)
at org.apache.catalina.security.SecurityUtil.execute(SecurityUtil.coffee:314)
at org.apache.catalina.security.SecurityUtil.doAsPrivilege(SecurityUtil.java:253)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.coffee:190)
at org.apache.catalina.cadre.ApplicationFilterChain.access$000(ApplicationFilterChain.java:46)
at org.apache.catalina.cadre.ApplicationFilterChain$1.run(ApplicationFilterChain.java:148)
at org.apache.catalina.cadre.ApplicationFilterChain$1.run(ApplicationFilterChain.java:144)
at java.security.AccessController.doPrivileged(Native Method)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:143)
at blackboard.auth.provider.saml.customization.filter.BbSAMLExceptionHandleFilter.doFilterInternal(BbSAMLExceptionHandleFilter.coffee:30)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
[SNIP]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:617)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at coffee.lang.Thread.run(Thread.java:745)
Caused by: org.opensaml.common.SAMLException: Response has invalid condition code urn:haven:names:tc:SAML:two.0:status:Responder, status message is nil
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.coffee:113)
at blackboard.auth.provider.saml.customization.consumer.BbSAMLWebSSOProfileConsumerImpl.processAuthenticationResponse(BbSAMLWebSSOProfileConsumerImpl.java:40)
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:87)
... 230 more
2016-11-01 12:47:19 -0500 - BbSAMLExceptionHandleFilter - javax.servlet.ServletException: Unsuccessful Authentication
at blackboard.auth.provider.saml.customization.filter.BbSAMLProcessingFilter.unsuccessfulAuthentication(BbSAMLProcessingFilter.java:31)
at org.springframework.security.spider web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.coffee:235)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
at org.springframework.spider web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.asking.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.coffee:53)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.spider web.FilterChainProxy.doFilter(FilterChainProxy.java:176)
at org.springframework.spider web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.coffee:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:262)
at sun.reflect.GeneratedMethodAccessor929.invoke(Unknown Source)
at sun.reverberate.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.coffee:498)
at org.apache.catalina.security.SecurityUtil$one.run(SecurityUtil.java:282)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.java:279)
at coffee.security.AccessController.doPrivileged(Native Method)
at javax.security.auth.Subject.doAsPrivileged(Subject.java:549)
at org.apache.catalina.security.SecurityUtil.execute(SecurityUtil.java:314)
at org.apache.catalina.security.SecurityUtil.doAsPrivilege(SecurityUtil.java:253)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:190)
at org.apache.catalina.core.ApplicationFilterChain.access$000(ApplicationFilterChain.coffee:46)
at org.apache.catalina.core.ApplicationFilterChain$1.run(ApplicationFilterChain.java:148)
at org.apache.catalina.core.ApplicationFilterChain$1.run(ApplicationFilterChain.java:144)
at java.security.AccessController.doPrivileged(Native Method)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:143)
at blackboard.auth.provider.saml.customization.filter.BbSAMLExceptionHandleFilter.doFilterInternal(BbSAMLExceptionHandleFilter.java:xxx)
[SNIP]
Resolution
- Navigate to the Admin Panel.
- Under Building Blocks, select Building Blocks.
- Select Installed Tools.
- Locate Authentication Provider - SAML in the list. Open the menu and select Settings.
- Under Signature Algorithm Settings, cull SHA-256 in the listing. After y'all select the Signature Algorithm Blazon, restart the SAML building cake to apply the new settings.
- Select Submit to save your changes.
Problem #v
Later on entering the login credentials on the ADFS login page, an fault may exist displayed after being redirected to the Blackboard Learn GUI: The specified resources was not found, or you practise not have permission to admission it or Sign On Error!
With the post-obit exceptions in the bb-services log:
2017-01-04 22:52:58 -0700 - unsuccessfulAuthentication - org.springframework.security.hallmark.AuthenticationServiceException: Error validating SAML message
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:100)
at org.springframework.security.authentication.ProviderManager.authenticate(ProviderManager.java:167)
at org.springframework.security.saml.SAMLProcessingFilter.attemptAuthentication(SAMLProcessingFilter.java:87)
at org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.coffee:217)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.coffee:184)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.coffee:64)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.asking.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.coffee:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:176)
at org.springframework.spider web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.spider web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.coffee:262)
at sun.reflect.GeneratedMethodAccessor935.invoke(Unknown Source)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at coffee.lang.reverberate.Method.invoke(Method.java:498)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.java:282)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.coffee:279)
at java.security.AccessController.doPrivileged(Native Method)
at javax.security.auth.Field of study.doAsPrivileged(Subject.java:549)
at org.apache.catalina.security.SecurityUtil.execute(SecurityUtil.java:314)
at org.apache.catalina.security.SecurityUtil.doAsPrivilege(SecurityUtil.java:253)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:190)
at org.apache.catalina.core.ApplicationFilterChain.access$000(ApplicationFilterChain.coffee:46)
at org.apache.catalina.core.ApplicationFilterChain$1.run(ApplicationFilterChain.java:148)
at org.apache.catalina.core.ApplicationFilterChain$1.run(ApplicationFilterChain.java:144)
at java.security.AccessController.doPrivileged(Native Method)
at org.apache.catalina.cadre.ApplicationFilterChain.doFilter(ApplicationFilterChain.coffee:143)
at blackboard.auth.provider.saml.customization.filter.BbSAMLExceptionHandleFilter.doFilterInternal(BbSAMLExceptionHandleFilter.coffee:xxx)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
[SNIP]
at org.apache.tomcat.util.net.SocketProcessorBase.run(SocketProcessorBase.java:49)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1142)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:617)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.java:745)
Caused past: org.opensaml.common.SAMLException: NameID element must be nowadays every bit part of the Subject in the Response message, please enable it in the IDP configuration
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.java:252)
at blackboard.auth.provider.saml.customization.consumer.BbSAMLWebSSOProfileConsumerImpl.processAuthenticationResponse(BbSAMLWebSSOProfileConsumerImpl.java:twoscore)
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:87)
... 214 more than
Every bit stated in the above SAML exception, the NameID element is missing from the Subject in the Response message. The problem typically occurs when the NameID is not setup as an Outgoing Merits Type in a Claims Rule for the Relying Political party Trust on the institution's ADFS IdP or the Claims Rule for the NameID is not in the proper order for the Relying Party Trust on the establishment'south ADFS IdP, which in plow causes the missing NameID element in the Subject in the Response bulletin.
Case: NameID element is missing
<Field of study>
<SubjectConfirmation Method="urn:oasis:names:tc:SAML:2.0:cm:bearer">
<SubjectConfirmationData InResponseTo="a22ai8iig0f75ae22hd28748b12da50"
NotOnOrAfter="2017-01-03T05:57:58.234Z"
Recipient="https://yourschool.blackboard.com/auth-saml/saml/SSO"
/>
</SubjectConfirmation>
</Subject>
Case: NameID element is present
<Subject>
<NameID Format="urn:oasis:names:tc:SAML:i.1:nameid-format:emailAddress">testadfs</NameID>
<SubjectConfirmation Method="urn:haven:names:tc:SAML:2.0:cm:bearer">
<SubjectConfirmationData InResponseTo="a5903d39if463ea87ieiab5135j9ji"
NotOnOrAfter="2017-01-05T04:33:12.715Z"
Recipient="https://yourschool.blackboard.com/auth-saml/saml/SSO"
/>
</SubjectConfirmation>
</Subject>
You tin can use the Firefox SAML tracer Add together-on to view the Subject in the Response message.
Resolution
In that location are three methods to resolving this issue.
- Ostend the steps from the SAML B2 Setup Guide for ADFS were properly followed and make changes as needed to transform an incoming claim for the Relying Political party Trust for their ADFS IdP:
- Select Edit Claims Rule.
- Select Add Rule.
- On the Select Rule Template page, select Transform an Incoming Claim for the Claim rule template and then select Next.
- On the Configure Rule folio, in the Claim rule name field, type Transform Email to Name ID.
- Incoming claim blazon should exist SamAccountName (it must match the Outgoing Claim Type created initially in the Transform Username to NameID dominion).
- The Outgoing claim type is Name ID.
- The Approachable name ID format is Electronic mail.
- Ostend Pass through all claim values is selected and select Terminate.
- Select OK to salve the rule and OK over again to complete the aspect mappings.
- Ensure for the order of the Claims Rules used for their ADFS IdP that the rule which has the NameID chemical element does not have whatsoever optional rules occurring before it.
- If using a custom attribute, ensure the NameID element is in the Relying Party Trust since Acquire still expects that their ADFS IdP release a NameID value.
Problem #6
When logged into Blackboard Learn via SAML hallmark, the user attempts to log out by clicking on the Sign Out button on the left side of the page and then clicks the End SSO Session button, a Sign On Error! is immediately displayed.
Sign On Error!
Blackboard Acquire is currently unable to log into your account using unmarried sign-on. Contact your administrator for assistance.
For reference, the Error ID is [error ID].
With the following exception in the bb-services log:
2017-05-08 fifteen:10:46 -0400 - BbSAMLExceptionHandleFilter Fault Id: f3299757-8d4e-4fab-98cf-49cd99f4891e - javax.servlet.ServletException: Incoming SAML message failed security validation
at org.springframework.security.saml.SAMLLogoutProcessingFilter.processLogout(SAMLLogoutProcessingFilter.java:145)
at org.springframework.security.saml.SAMLLogoutProcessingFilter.doFilter(SAMLLogoutProcessingFilter.java:104)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.coffee:64)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.coffee:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.spider web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.spider web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
[SNIP]
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.java:745)
Caused past: org.opensaml.ws.security.SecurityPolicyException: Validation of asking uncomplicated signature failed for context issuer
at org.opensaml.common.binding.security.BaseSAMLSimpleSignatureSecurityPolicyRule.doEvaluate(BaseSAMLSimpleSignatureSecurityPolicyRule.coffee:139)
at org.opensaml.common.binding.security.BaseSAMLSimpleSignatureSecurityPolicyRule.evaluate(BaseSAMLSimpleSignatureSecurityPolicyRule.coffee:103)
at org.opensaml.ws.security.provider.BasicSecurityPolicy.evaluate(BasicSecurityPolicy.java:51)
at org.opensaml.ws.message.decoder.BaseMessageDecoder.processSecurityPolicy(BaseMessageDecoder.java:132)
at org.opensaml.ws.bulletin.decoder.BaseMessageDecoder.decode(BaseMessageDecoder.java:83)
at org.opensaml.saml2.bounden.decoding.BaseSAML2MessageDecoder.decode(BaseSAML2MessageDecoder.java:70)
at org.springframework.security.saml.processor.SAMLProcessorImpl.retrieveMessage(SAMLProcessorImpl.java:105)
at org.springframework.security.saml.processor.SAMLProcessorImpl.retrieveMessage(SAMLProcessorImpl.coffee:172)
at org.springframework.security.saml.SAMLLogoutProcessingFilter.processLogout(SAMLLogoutProcessingFilter.coffee:131)
... 244 more than
The mistake occurs because of the Unmarried Logout Service Type setting on the SAML Settings page.
Resolution
The setting needs to be configured in Blackboard Learn and on the ADFS server.
For ADFS every bit the IdP, select the Post setting only and remove the Redirect endpoint for the Acquire instance'due south Relying Party Trust on the ADFS server.
- In Learn, navigate to Admin > Authentication > (Provider Proper noun) > SAML Settings > Single Logout Service Type.
- Select Post and clear the Redirect checkbox.
- In the ADFS Server, go into the Relying Party Trust for your Learn Instance.
- Select Backdrop > Endpoints. Two SAML logout endpoints are listed.
- Remove the Redirect endpoint. Select Remove Endpoint to remove it, then Use and OK.
After making the above changes in Learn and the ADFS server, the End SSO Session logout push volition work to properly sign out the user.
Problem #seven
Later on entering the login credentials on the ADFS login page, a Sign On Fault! bulletin is displayed when redirected to Acquire.
With the following SAML exception in the bb-services log:
2017-05-26 07:39:30 -0400 - unsuccessfulAuthentication - org.springframework.security.hallmark.AuthenticationServiceException: Error validating SAML message
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:100)
at org.springframework.security.authentication.ProviderManager.authenticate(ProviderManager.java:167)
at org.springframework.security.saml.SAMLProcessingFilter.attemptAuthentication(SAMLProcessingFilter.coffee:87)
at blackboard.auth.provider.saml.customization.filter.BbSAMLProcessingFilter.attemptAuthentication(BbSAMLProcessingFilter.coffee:46)
at org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.java:217)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.spider web.FilterChainProxy.doFilter(FilterChainProxy.java:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.coffee:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53)
at org.springframework.spider web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.spider web.FilterChainProxy.doFilter(FilterChainProxy.coffee:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.coffee:262)
at sun.reflect.GeneratedMethodAccessor380.invoke(Unknown Source)
at sun.reverberate.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.coffee:43)
at coffee.lang.reflect.Method.invoke(Method.java:498)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.coffee:282)
at org.apache.catalina.security.SecurityUtil$ane.run(SecurityUtil.java:279)
at java.security.AccessController.doPrivileged(Native Method)
at javax.security.auth.Subject.doAsPrivileged(Subject area.java:549)
at org.apache.catalina.security.SecurityUtil.execute(SecurityUtil.java:314)
at org.apache.catalina.security.SecurityUtil.doAsPrivilege(SecurityUtil.coffee:253)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.coffee:190)
at org.apache.catalina.cadre.ApplicationFilterChain.admission$000(ApplicationFilterChain.java:46)
at org.apache.catalina.core.ApplicationFilterChain$ane.run(ApplicationFilterChain.java:148)
at org.apache.catalina.core.ApplicationFilterChain$1.run(ApplicationFilterChain.java:144)
at java.security.AccessController.doPrivileged(Native Method)
at org.apache.catalina.cadre.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:143)
at blackboard.auth.provider.saml.customization.filter.BbSAMLExceptionHandleFilter.doFilterInternal(BbSAMLExceptionHandleFilter.coffee:37)
[SNIP]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.coffee:617)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.java:745)
Caused by: org.opensaml.mutual.SAMLException: Response has invalid status code urn:oasis:names:tc:SAML:2.0:condition:Responder, status message is null
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.coffee:113)
at blackboard.auth.provider.saml.customization.consumer.BbSAMLWebSSOProfileConsumerImpl.processAuthenticationResponse(BbSAMLWebSSOProfileConsumerImpl.java:56)
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:87)
... 247 more than
Resolution
Beginning in Blackboard Learn 3200.0.0, in that location is at present an pick to regenerate the SAML encryption document by navigating to System Admin > Building Blocks > Authentication Provider - SAML > Settings > Regenerate Document. The Sign On Error! trouble may occur if the Regenerate document button is selected subsequently the SP metadata is already uploaded to the Relying Party Trust for the Learn site on the ADFS server. To resolve the issue:
- Navigate to Arrangement Admin > Authentication > [SAML Provider Name] > SAML Settings.
- Select Generate adjacent to Service Provider Metadata to relieve the new metadata file.
- Access your ADFS server and upload the new SP metadata to the Relying Political party Trust for your Learn site.
If y'all generate a new certificate under the B2 settings, yous need to toggle the SAML B2 to Inactive and and so back to Agile to strength the change. After, yous tin can return to the provider settings and generate the new metadata to import into the IDP. If you lot don't toggle the settings, the erstwhile certificate may still be included when y'all generate new metadata. The IDP won't be updated and the next fourth dimension Learn restarts it will present the new document. SAML authentication volition break because of this mismatch.
Federation Metadata
With Active Directory Federation Services (ADFS), since the metadata for an ADFS federation typically located in https://[ADFS Server Hostname]/FederationMetadata/2007-06/FederationMetadata.xml includes an element that is incompatible with SAML 2.0, the metadata needs to be edited to delete the incompatible element before it is uploaded to the Identity Provider Settings section on the SAML Authentication Settings page in the Blackboard Learn GUI. If the metadata with the incompatible element is uploaded, an error will occur when selecting the SAML login link on the Blackboard Learn login page: Metadata for entity [entity] and role {} wasn't establish. For reference, the Fault ID is [error ID].
And the corresponding Java stack trace for the Mistake ID in the bb-services log has the following:
2016-06-21 11:42:51 -0700 - Metadata for entity https://<Learn Server Hostname>/adfs/ls/ and part {urn:oasis:names:tc:SAML:2.0:metadata}SPSSODescriptor wasn't found<P><span class="captionText">For reference, the Error ID is c99511ae-1162-4941-b823-3dda19fea157.</span> - org.opensaml.saml2.metadata.provider.MetadataProviderException: Metadata for entity https://ulvsso.laverne.edu/adfs/ls/ and role {urn:oasis:names:tc:SAML:2.0:metadata}SPSSODescriptor wasn't found
at org.springframework.security.saml.context.SAMLContextProviderImpl.populateLocalEntity(SAMLContextProviderImpl.java:319)
at org.springframework.security.saml.context.SAMLContextProviderImpl.populateLocalContext(SAMLContextProviderImpl.java:216)
at org.springframework.security.saml.context.SAMLContextProviderImpl.getLocalAndPeerEntity(SAMLContextProviderImpl.java:126)
at org.springframework.security.saml.SAMLEntryPoint.embark(SAMLEntryPoint.java:146)
at org.springframework.security.saml.SAMLEntryPoint.doFilter(SAMLEntryPoint.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.coffee:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.coffee:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.coffee:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.coffee:262)
at lord's day.reflect.GeneratedMethodAccessor1652.invoke(Unknown Source)
at lord's day.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.coffee:498)
[SNIP]
Resolution
Since the default metadata location for an ADFS federation is https://[ADFS server hostname]/FederationMetadata/2007-06/FederationMetadata.xml:
- Download this file and open it in a text editor. Advisedly delete the section starting <ds:Signature xmlns:ds="http://world wide web.w3.org/2000/09/xmldsig#"> ... </X509Data></KeyInfo> and ending </ds:Signature>
<ds:Signature xmlns:ds="http://www.w3.org/2000/09/xmldsig#"><ds:SignedInfo>
<ds:CanonicalizationMethod Algorithm="http://www.w3.org/2001/10/xml-exc-c14n#"/>
<ds:SignatureMethod Algorithm="http://www.w3.org/2001/04/xmldsig-more#rsa-sha256"/>
<ds:Reference URI="#_43879f32-9a91-4862-bc87-e98b85b51158">
<ds:Transforms>
<ds:Transform Algorithm="http://www.w3.org/2000/09/xmldsig#enveloped-signature"/>
<ds:Transform Algorithm="http://www.w3.org/2001/x/xml-exc-c14n#"/>
</ds:Transforms>
<ds:DigestMethod Algorithm="http://www.w3.org/2001/04/xmlenc#sha256"/>
<ds:DigestValue>z1H1[SNIP]jaYM=</ds:DigestValue>
</ds:Reference>
</ds:SignedInfo>
<ds:SignatureValue> FVj[SNIP]edrfNKWvsvk5A==
</ds:SignatureValue>
<KeyInfo xmlns="http://www.w3.org/2000/09/xmldsig#">
<X509Data>
<X509Certificate>
FDdd[SNIP]qTNKdk5F/vf1AocDaX
</X509Certificate>
</X509Data>
</KeyInfo>
</ds:Signature> - Upload the updated metadata XML file in the Blackboard Larn GUI on the SAML Hallmark Settings page in the Identity Provider Settings department.
- Toggle the SAML authentication provider and SAML B2 Inactive/Available, while having the SAML hallmark provider in 'Active' status.
If an institution is testing SAML hallmark on a Blackboard Learn site and has multiple SAML authentication providers that share the same underlying ADFS IdP metadata XML file on the Blackboard Acquire site, even if the other SAML authentication providers are set to Inactive, they will also need to have the updated metadata XML file uploaded in the Blackboard Learn GUI on the SAML Authentication Settings page in the Identity Provider Settings section. The SAML B2 should then be toggled Inactive/Available, while having the SAML hallmark provider in 'Active' status, to ensure the updated metadata XML file is recognized system-broad.
Incorrect user lookup method
Afterwards entering the login credentials on the ADFS login folio, the user is redirected to the Blackboard Learn GUI, merely non logged into Blackboard Learn.
The ONLY SAML hallmark related outcome in the bb-services log is:
2016-10-18 thirteen:03:28 -0600 - userName is zero or empty
Resolution
- Login to Blackboard Larn as administrator using the default Blackboard Acquire Internal authentication.
- Navigate to System Admin > "SAML Authentication Provider Name" > Edit.
- Change the User Lookup Method from Batch Uid to Username.
Extra Cease SSO Session logout button
ADFS tries to add an extra End SSO Session logout button on the End all sessions? folio that is displayed later on first selecting the logout push at the acme correct in the Blackboard Learn GUI.
This is done past adding an actress SingleLogoutService to the IdP Metadata file:
<SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://your.server.proper name/adfs/ls/"/>
<SingleLogoutService Binding="urn:haven:names:tc:SAML:2.0:bindings:HTTP-POST" Location="https://your.server.proper name/adfs/ls/"/>
Since that is an optional SAML B2 IdP configuration and the signature being provided in the Redirect Endpoint is not correct, an mistake will occur when selecting the extra Finish SSO Session button on the End all sessions? page: Incoming SAML message failed security validation. Validation of request uncomplicated signature failed for context issuer. For reference, the mistake Id is [error ID].
The respective Java stack trace for the Error ID in the bb-services log has:
2016-10-17 xvi:57:44 -0400 - Incoming SAML message failed security validation Validation of request simple signature failed for context issuer<P><bridge course="captionText">For reference, the Mistake ID is 930c7767-8710-475e-8415-2077152280e0.</span> - org.opensaml.ws.security.SecurityPolicyException: Validation of request uncomplicated signature failed for context issuer
at org.opensaml.mutual.bounden.security.BaseSAMLSimpleSignatureSecurityPolicyRule.doEvaluate(BaseSAMLSimpleSignatureSecurityPolicyRule.java:139)
at org.opensaml.common.binding.security.BaseSAMLSimpleSignatureSecurityPolicyRule.evaluate(BaseSAMLSimpleSignatureSecurityPolicyRule.java:103)
at org.opensaml.ws.security.provider.BasicSecurityPolicy.evaluate(BasicSecurityPolicy.java:51)
at org.opensaml.ws.bulletin.decoder.BaseMessageDecoder.processSecurityPolicy(BaseMessageDecoder.java:132)
at org.opensaml.ws.bulletin.decoder.BaseMessageDecoder.decode(BaseMessageDecoder.java:83)
at org.opensaml.saml2.bounden.decoding.BaseSAML2MessageDecoder.decode(BaseSAML2MessageDecoder.java:70)
at org.springframework.security.saml.processor.SAMLProcessorImpl.retrieveMessage(SAMLProcessorImpl.java:105)
at org.springframework.security.saml.processor.SAMLProcessorImpl.retrieveMessage(SAMLProcessorImpl.java:172)
at org.springframework.security.saml.SAMLLogoutProcessingFilter.processLogout(SAMLLogoutProcessingFilter.coffee:131)
at org.springframework.security.saml.SAMLLogoutProcessingFilter.doFilter(SAMLLogoutProcessingFilter.java:104)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.coffee:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.coffee:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.spider web.FilterChainProxy.doFilter(FilterChainProxy.coffee:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:262)
at sun.reflect.GeneratedMethodAccessor1652.invoke(Unknown Source)
at sun.reverberate.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
[SNIP]
Resolution
- Access the ADFS Server and get into the Relying Party Trust for the Blackboard Learn Case.
- Select Properties > Endpoints tab.
- In the Endpoints tab there will be 2 SAML Logout Endpoints.
- Remove the Redirect endpoint.
- Select Remove Endpoint to remove it, and so Employ and OK.
After removing the Redirect endpoint, the End SSO Session button will work properly signing out the user.
Viewing application logs with event viewer
When troubleshooting an ADFS SAML authentication issue, information technology may be necessary to also have an institution review the ADFS application logs in the Event Viewer on their ADFS server for further insight. This is peculiarly necessary when the SAML response from the ADFS server has a Request Denied condition as seen below:
<samlp:Status>
<samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Responder">
<samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:RequestDenied" />
</samlp:StatusCode>
</samlp:Condition>
The SAML response tin can be viewed by using the Firefox browser SAML tracer Addition.
The Request Denied status in a response typically indicates a problem occurred when the IdP (ADFS) attempted to understand the response and procedure the result the SP (Blackboard Learn) provided.
To view the ADFS awarding logs with the Outcome Viewer:
- Open up the Event Viewer on the ADFS server.
- On the View card, select Show Analytic and Debug Logs.
- In the console tree, navigate to Application and Service Logs > Ad FS Tracing > Debug.
Azure Agile Directory
Azure AD is Microsoft'due south (MS) cloud based directory and identity direction service.
Ship first part of e-mail
If an institution is using Azure AD as their IdP and wishes to only have the first part of the Azure Advertizing email username used for the Blackboard Larn username, they can configure their Azure Advertising IdP to use the special ExtractMailPrefix() function to remove the domain suffix from either the email or the user principal name resulting in only the showtime part of the username beingness passed through (e.g. "joesmith" instead of joesmith@example.com).
If the Blackboard Learn Remote User ID is urn:oid:one.iii.6.one.4.1.5923.one.1.one.6, the Attribute setting for the Azure IdP would look like this:
Aspect Proper name: urn:oid:i.3.6.i.4.1.5923.1.i.1.6
Attribute Value: ExtractMailPrefix()
Mail: user.userprincipalname
So with the case joesmith@instance.com email username, information technology would exist passed like this in the SAML assertion from the Azure IdP to Blackboard Acquire:
<Attribute Proper name="urn:oid:1.3.6.1.4.one.5923.1.1.1.6">
<AttributeValue>joesmith</AttributeValue>
Additional info nearly using the ExtractMailPrefix() function is available on the MS Azure documentation page.
Azure Advertising IdP updating certificate
After entering the login credentials on the MS Azure AD login page, a Sign On Error! may exist displayed later on being redirected to the Blackboard Learn GUI.
With the following exception in the bb-services log:
2016-10-13 12:03:23 +0800 - unsuccessfulAuthentication - org.springframework.security.authentication.AuthenticationServiceException: Error validating SAML message
at org.springframework.security.saml.SAMLAuthenticationProvider.authenticate(SAMLAuthenticationProvider.java:100)
at org.springframework.security.authentication.ProviderManager.authenticate(ProviderManager.java:167)
at org.springframework.security.saml.SAMLProcessingFilter.attemptAuthentication(SAMLProcessingFilter.coffee:87)
at org.springframework.security.spider web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.java:217)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
at org.springframework.spider web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.coffee:330)
at org.springframework.security.spider web.context.request.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.java:53)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.java:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.spider web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.java:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:262)
at sun.reverberate.GeneratedMethodAccessor854.invoke(Unknown Source)
at sunday.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.coffee:43)
at java.lang.reflect.Method.invoke(Method.coffee:498)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.coffee:282)
at org.apache.catalina.security.SecurityUtil$ane.run(SecurityUtil.java:279)
at java.security.AccessController.doPrivileged(Native Method)
at javax.security.auth.Subject.doAsPrivileged(Subject.java:549)
at org.apache.catalina.security.SecurityUtil.execute(SecurityUtil.java:314)
at org.apache.catalina.security.SecurityUtil.doAsPrivilege(SecurityUtil.java:253)
at org.apache.catalina.cadre.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.java:190)
at org.apache.catalina.core.ApplicationFilterChain.access$000(ApplicationFilterChain.java:46)
at org.apache.catalina.core.ApplicationFilterChain$1.run(ApplicationFilterChain.java:148)
at org.apache.catalina.core.ApplicationFilterChain$one.run(ApplicationFilterChain.coffee:144)
at coffee.security.AccessController.doPrivileged(Native Method)
at org.apache.catalina.core.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:143)
at blackboard.auth.provider.saml.customization.filter.BbSAMLExceptionHandleFilter.doFilterInternal(BbSAMLExceptionHandleFilter.java:thirty)
[SNIP]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:617)
at org.apache.tomcat.util.threads.TaskThread$WrappingRunnable.run(TaskThread.java:61)
at java.lang.Thread.run(Thread.coffee:745)
Caused by: org.opensaml.common.SAMLException: Response doesn't have whatsoever valid assertion which would pass subject validation
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.java:229)
at blackboard.auth.provider.saml.customization.consumer.BbSAMLWebSSOProfileConsumerImpl.processAuthenticationResponse(BbSAMLWebSSOProfileConsumerImpl.java:40)
at org.springframework.security.saml.SAMLAuthenticationProvider.cosign(SAMLAuthenticationProvider.coffee:87)
... 230 more than
Caused by: org.opensaml.xml.validation.ValidationException: Signature is not trusted or invalid
at org.springframework.security.saml.websso.AbstractProfileBase.verifySignature(AbstractProfileBase.java:272)
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.verifyAssertionSignature(WebSSOProfileConsumerImpl.coffee:419)
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.verifyAssertion(WebSSOProfileConsumerImpl.java:292)
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.java:214)
... 232 more
This is caused by the MS Azure Ad IdP updating the certificate, but the metadata XML used past the Blackboard Learn SP non being adjusted to reflect the new certificate.
Resolution
- The new metadata XML file with the new certificate volition need to exist updated on the SAML Settings folio in the Blackboard Learn GUI for the authentication provider.
- The SAML B2 and the authentication provider will then demand to be toggled Inactive/Bachelor, while having the SAML authentication provider in 'Active' status, to have the updated metadata with the new certificate applied.
- If a Blackboard Learn site has multiple authentication providers that share the same underlying document for the aforementioned underlying IdP Entity ID, ALL those authentication providers will need to be updated.
Microsoft has indicated that that they volition be updating certificates every half-dozen weeks from now on, and that such updates volition exist unannounced.
IdP-initiated single sign on
If a user first logs into their user portal and then selects the app for their Blackboard Learn site, a new browser tab opens to display a message: The specified resource was not found, or you do not have permission to admission it.
With the corresponding SAML related events in the stdout-stderr.log:
INFO | jvm 1 | 2016/08/xvi 10:49:22 | - /saml/SSO at position one of 10 in additional filter chain; firing Filter: 'SecurityContextPersistenceFilter'
INFO | jvm ane | 2016/08/16 ten:49:22 | - HttpSession returned null object for SPRING_SECURITY_CONTEXT
INFO | jvm ane | 2016/08/sixteen 10:49:22 | - No SecurityContext was available from the HttpSession: [email protected] A new one will be created.
INFO | jvm 1 | 2016/08/16 x:49:22 | - /saml/SSO at position 2 of 10 in additional filter concatenation; firing Filter: 'WebAsyncManagerIntegrationFilter'
INFO | jvm one | 2016/08/sixteen 10:49:22 | - /saml/SSO at position 3 of 10 in additional filter concatenation; firing Filter: 'HeaderWriterFilter'
INFO | jvm 1 | 2016/08/16 10:49:22 | - /saml/SSO at position iv of ten in additional filter chain; firing Filter: 'FilterChainProxy'
INFO | jvm 1 | 2016/08/16 10:49:22 | - Checking match of asking : '/saml/sso'; against '/saml/login/**'
INFO | jvm ane | 2016/08/xvi x:49:22 | - Checking match of asking : '/saml/sso'; against '/saml/logout/**'
INFO | jvm ane | 2016/08/16 10:49:22 | - Checking match of request : '/saml/sso'; against '/saml/bbsamllogout/**'
INFO | jvm 1 | 2016/08/16 10:49:22 | - Checking lucifer of request : '/saml/sso'; against '/saml/sso/**'
INFO | jvm 1 | 2016/08/xvi 10:49:22 | - /saml/SSO at position 1 of 1 in additional filter chain; firing Filter: 'SAMLProcessingFilter'
INFO | jvm 1 | 2016/08/16 10:49:22 | - Forwarding to /
INFO | jvm ane | 2016/08/16 10:49:22 | - DispatcherServlet with name 'saml' processing POST request for [/auth-saml/saml/SSO]
INFO | jvm 1 | 2016/08/xvi ten:49:22 | - No mapping institute for HTTP request with URI [/auth-saml/saml/SSO] in DispatcherServlet with name 'saml'
INFO | jvm 1 | 2016/08/16 x:49:22 | - SecurityContext is empty or contents are anonymous - context will not exist stored in HttpSession.
INFO | jvm one | 2016/08/sixteen 10:49:22 | - Successfully completed request
INFO | jvm ane | 2016/08/16 10:49:22 | - Skip invoking on
INFO | jvm i | 2016/08/16 10:49:22 | - SecurityContextHolder now cleared, as request processing completed
The Service Provider Settings section of the SAML Hallmark Settings folio has changed and the Enable automatic SSO pick should be checked to allow a user to access Blackboard Larn from their portal. If it is enabled, the ACS URL volition too be changed to include an allonym.
Incorrect certificate error
Subsequently entering the login credentials on the SAML authentication provider login page, a Sign On Error! may exist displayed after being redirected to the Blackboard Learn GUI.
With the post-obit DOMException and WRONG_DOCUMENT_ERR in the bb-services log:
2016-11-18 12:27:31 -0600 - WRONG_DOCUMENT_ERR: A node is used in a different document than the i that created it.<P><span class="captionText">For reference, the Error ID is 86ebb81d-d3a3-4da5-95ab-1c94505f4281.</bridge> - org.w3c.dom.DOMException: WRONG_DOCUMENT_ERR: A node is used in a different document than the one that created it.
at org.apache.xerces.dom.ParentNode.internalInsertBefore(Unknown Source)
at org.apache.xerces.dom.ParentNode.insertBefore(Unknown Source)
at org.apache.xerces.dom.NodeImpl.appendChild(Unknown Source)
at org.opensaml.xml.encryption.Decrypter.parseInputStream(Decrypter.coffee:832)
at org.opensaml.xml.encryption.Decrypter.decryptDataToDOM(Decrypter.java:610)
at org.opensaml.xml.encryption.Decrypter.decryptUsingResolvedEncryptedKey(Decrypter.java:795)
at org.opensaml.xml.encryption.Decrypter.decryptDataToDOM(Decrypter.java:535)
at org.opensaml.xml.encryption.Decrypter.decryptDataToList(Decrypter.java:453)
at org.opensaml.xml.encryption.Decrypter.decryptData(Decrypter.java:414)
at org.opensaml.saml2.encryption.Decrypter.decryptData(Decrypter.java:141)
at org.opensaml.saml2.encryption.Decrypter.decrypt(Decrypter.java:69)
at org.springframework.security.saml.websso.WebSSOProfileConsumerImpl.processAuthenticationResponse(WebSSOProfileConsumerImpl.java:199)
at org.springframework.security.saml.SAMLAuthenticationProvider.cosign(SAMLAuthenticationProvider.java:82)
at org.springframework.security.authentication.ProviderManager.cosign(ProviderManager.java:167)
at org.springframework.security.saml.SAMLProcessingFilter.attemptAuthentication(SAMLProcessingFilter.java:87)
at org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter.doFilter(AbstractAuthenticationProcessingFilter.java:217)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.coffee:184)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.header.HeaderWriterFilter.doFilterInternal(HeaderWriterFilter.java:64)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.coffee:107)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.asking.async.WebAsyncManagerIntegrationFilter.doFilterInternal(WebAsyncManagerIntegrationFilter.coffee:53)
at org.springframework.web.filter.OncePerRequestFilter.doFilter(OncePerRequestFilter.coffee:107)
at org.springframework.security.spider web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.context.SecurityContextPersistenceFilter.doFilter(SecurityContextPersistenceFilter.java:91)
at org.springframework.security.web.FilterChainProxy$VirtualFilterChain.doFilter(FilterChainProxy.java:330)
at org.springframework.security.web.FilterChainProxy.doFilterInternal(FilterChainProxy.java:213)
at org.springframework.security.web.FilterChainProxy.doFilter(FilterChainProxy.coffee:176)
at org.springframework.web.filter.DelegatingFilterProxy.invokeDelegate(DelegatingFilterProxy.java:346)
at org.springframework.web.filter.DelegatingFilterProxy.doFilter(DelegatingFilterProxy.java:262)
at sun.reflect.GeneratedMethodAccessor1209.invoke(Unknown Source)
at sunday.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.apache.catalina.security.SecurityUtil$1.run(SecurityUtil.java:277)
at org.apache.catalina.security.SecurityUtil$ane.run(SecurityUtil.java:274)
at java.security.AccessController.doPrivileged(Native Method)
at javax.security.auth.Field of study.doAsPrivileged(Subject.java:549)
at org.apache.catalina.security.SecurityUtil.execute(SecurityUtil.java:309)
at org.apache.catalina.security.SecurityUtil.doAsPrivilege(SecurityUtil.java:249)
at org.apache.catalina.core.ApplicationFilterChain.internalDoFilter(ApplicationFilterChain.coffee:237)
at org.apache.catalina.core.ApplicationFilterChain.access$000(ApplicationFilterChain.java:55)
at org.apache.catalina.core.ApplicationFilterChain$1.run(ApplicationFilterChain.java:191)
at org.apache.catalina.core.ApplicationFilterChain$i.run(ApplicationFilterChain.java:187)
at java.security.AccessController.doPrivileged(Native Method)
at org.apache.catalina.cadre.ApplicationFilterChain.doFilter(ApplicationFilterChain.java:186)
at blackboard.platform.servlet.DevNonceFilter.doFilter(DevNonceFilter.java:68)
[SNIP]
The reason the problem occurs is another B2/Projection changed the system property javax.xml.parsers.DocumentBuilderFactory value from org.apache.xerces.jaxp.DocumentBuilderFactoryImpl to com.sun.org.apache.xerces.internal.jaxp.DocumentBuilderFactoryImpl.
Temporary resolution
Until a fix is released, the temporary resolution options are:
- Restart Bb services on each node.
- Turn off SAML response encryption on the IdP side. As the whole communication is over SSL, this volition not reduce the security of the authentication.
No option to add SAML to Provider Order
When configuring SAML hallmark, an institution may find there is not an option to add a SAML authentication provider in the Provider Order section in Blackboard Larn GUI when navigating to System Admin > Building Blocks: Authentication > Provider Order.
The reason there is non an option to add a SAML authentication provider to the Provider Order is that redirect type providers such as CAS and SAML hand off authentication to the remote authentication source. Those are not listed in the Provider Order equally they are considered the authoritative source for authentication and handle their own authentication failures.
Test SAML connection
First with the Q4 2016 release of Blackboard Acquire, in that location is now an option to examination the connection for a SAML provider in the Authentication section in the Blackboard Learn GUI. The connection test will cheque the post-obit items:
- Parse IdP metadata
- Connect to IdP
- Receive SAML response
- Parse SAML response
- Remote User ID match
- Log in to Blackboard Learn
To test the connection for a SAML authentication provider:
- Login to Blackboard Learn as an administrator.
- Navigate to Organisation Admin > Building Blocks: Authentication > "SAML Provider Proper noun" > Test Connection.
- Enter the IdP login credentials if prompted.
The Test Connection feature can be used in lieu of manually enabling SAML debug logging in Blackboard Learn for multiple reasons.
The Identity Provider Entity ID value that is displayed on the Test Connectedness output page is pulled from the Issuer element in the SAML POST from the IdP to Blackboard Acquire after the user has been authenticated:
<Issuer xmlns="urn:haven:names:tc:SAML:two.0:assertion">http://bbpdcsi-adfs1.bbpdcsi.local/a...services/trust</Issuer>
The SAML Attribute values displayed on the Test Connectedness output page in the SAML Response department are pulled from the Bailiwick and AttributeStatement elements in the SAML Post from the IdP to Blackboard Learn later the user has been authenticated:
<Field of study>
<NameID Format="urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress">luke.skywalker</NameID>
[SNIP]
</Subject field>
<AttributeStatement>
<Attribute Name="SamAccountName">
<AttributeValue>luke.skywalker</AttributeValue>
</Attribute>
<Attribute Name="urn:oid:2.v.four.42">
<AttributeValue>Luke</AttributeValue>
</Attribute>
<Attribute Name="urn:oid:two.5.four.4">
<AttributeValue>Skywalker</AttributeValue>
</Attribute>
</AttributeStatement>
Create a SAML hallmark provider and IdP for testing
Use the steps below to create an Identity Provider (IdP) using Centrify'southward free SSO authentication solution.
That IdP can and then be configured equally the SAML authentication provider in a Blackboard Learn Service Provider (SP):
Blackboard Learn Service Provider
- Login to the Blackboard Learn GUI as an administrator and navigate to System Admin > Authentication.
- Select Create Provider > SAML.
- Input the post-obit settings:
- Name > SAML or anything you want.
- Authentication Provider > Inactive (for now).
- User Lookup Method > Username
- Restrict by Hostname > Utilise this provider for any hostnames
- Link Text > SAML Centrify Login
- Select Save and Configure.
- In the Entity ID field, set up this to anything you want (only if you modify it you must provide the updated Service Provider Metadata to the Identity Provider). Simply copy/paste the ACS URL.
- Under Service Provider Metadata, select Generate and save the file to your desktop.
- Under Data Source, it is recommended to create a new Data Source for this named CENTRIFY, otherwise use SYSTEM or whatever you choose
- Next to Enable JIT Provisioning, bank check this box and then that an account is automatically created when attempting to login via this SAML hallmark provider if the user does not exist. If JIT Provisioning is non selected, the user in Blackboard Learn will need to be created manually.
- In the Compatible Data Sources listing, be sure to select the data sources that this authentication provider should be compatible with.
- Select Point Identity Provider for the Identity Provider Type.
- Skip the Identity Provider Metadata for now, you will upload the file after it has been created in the Centrify IdP section.
- For the Map SAML Attributes section, use NameID for the Remote User ID.
- Select Submit.
Centrify Identity Provider
- Go to the Centrify website and select Start At present.
- Enter your information to sign upwardly and select Start Now.
- You volition receive a welcome email with your admin credentials. Utilize them to log in to https://cloud.centrify.com.
- Select Skip on the Welcome to Centrify Place Service window.
- In the Apps tab at the top of the page, select the Add Web Apps button.
- In the Custom tab, scroll down and select the Add button for SAML. Select Yes.
- Select Shut at the bottom of the Add Web Apps window.
- Get to the Apps tab. In the Application Settings section, select the Upload SP Metadata button and upload the file that was created in Step 6 of the Blackboard Learn SP section.
- The Assertion Consumer Service URL should automatically populate afterwards uploading the SP Metadata.
- Uncheck Encrypt Assertion. This allows the attributes being released from the IdP and sent to Blackboard Larn to be viewed using the Firefox browser SAML tracer Add-on or Chrome SAML Message Decoder. Equally the whole communication is over SSL this will non reduce the security of the authentication.
- Scroll downward and select Download Identity Provider SAML Metadata. Save the file to your desktop.
- Select Salvage and get to the next section.
- Enter a name for the Description department. Select Salve and go to the side by side section.
- In the User Access section, select Everybody and Organization Ambassador. Select Relieve.
- Do not make any selections in the Policy section.
- For the Business relationship Mapping section, ostend that userprincipalname is entered for the Directory Service field name.
- For the Avant-garde department, add the following line to the lesser of the script used to generate a SAML assertion for the application:
The complete script will be:
setIssuer(Issuer);
setSubjectName(UserIdentifier);
setAudience('https://YourLearnServer.blackboard.c...saml/saml/SSO');
setRecipient(ServiceUrl);
setHttpDestination(ServiceUrl);
setSignatureType('Assertion');
setNameFormat('emailaddress');
setAttribute("NameID", LoginUser.Get("userprincipalname"));Which will allow the Centrify IdP to release an AttributeStatement with the User ID in the SAML POST.
Example:
<AttributeStatement>
<Attribute Name="NameID"
NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:basic"
>
<AttributeValue>luke.skywalker@blackboard.com.47</AttributeValue>
</Attribute>
</AttributeStatement>More on specifying exclamation elements in the Centrify SAML script
- Select Relieve.
- No changes should need to be made to the remaining sections (App Gateway, Changelog and Workflow).
- In the Apps tab, confirm the SAML app was automatically deployed.
- In the Users tab, select Add together Users, enter the account info for a user, and select Create User.
- Log back into the Blackboard Larn GUI as an administrator, navigate to System Admin > Hallmark > SAML Authentication Provider Name > SAML Settings > Identity Provider Settings, upload the IdP Metadata file that was saved to your desktop in Step thirteen and select Submit.
The Centrify IdP user that was created can now login to Blackboard Learn via SAML past selecting that authentication provider on the login page, and logout of Blackboard Learn using the extra Stop SSO Session logout button on the Terminate all sessions? page that is displayed later selecting the logout push button at the top right of Blackboard Learn.
Change text on End SSO Session logout page
An institution may enquire if information technology is possible to modify the text on the Cease SSO Session logout page. It is possible to change the text on the End SSO Session logout page by editing the Language Pack:
- Open the Language Pack file.
- Navigate to auth-provider-saml/src/chief/webapp/Web-INF/bundles/bb-manifest-en_US.properties.
- Update the Message Keys:
saml.single.logout.warning.conent.description // the first line
saml.single.logout.warning.conent.recommend // 2nd line
saml.single.logout.alarm.endsso.title // 3rd line
saml.single.logout.alert.endsso.button // the button
saml.single.logout.warning.backtolearn // the cancel button
Redirect users to the IdP login page
The standard Blackboard Acquire login page presents username and password fields for the default Learn Internal authentication provider. When you lot enable SAML authentication, a small "Sign in using..." link for SAML appears at the lesser of this page, and so you lot may desire to redirect users to the IdP'due south hallmark server automatically when they access the Acquire login folio.
One option to attain this is to navigate to Organisation Admin > Authentication and set the default Learn Internal authentication to Inactive, which means a login page is no longer displayed, and immediately the user is redirected to the SAML login. The problem with that pick is that it overrides the default login URL and prevents any non-SAML user to login.
To avoid this event and provide almost the same issue, use a Custom Login Page. Users are redirected to the SAML authentication provider's IdP login page, simply the default login link is as well usable.
- Ensure the default Larn Internal hallmark is agile
- On the default login page, copy the location of the provider redirect east.yard. Sign in using... SAML. Right-click on the link and select Copy Link Location.
- Navigate to System Admin > Communities > Brands and Themes > Customize Login Page.
- Select Download adjacent to Default Login Page to download the default login JSP file.
- Open the JSP file with a text editor. Add the following sample HTML to the login JSP file and replace the URL text with the URL that was copied in Stride 2.
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML iv.0 Transitional//EN">
<html>
<head>
<title>Blackboard Learn - Redirect</title>
<meta http-equiv="REFRESH" content="0;url=https://URL_Goes_Here"></HEAD>
<BODY style="font-family: arial,sans-serif;font-size: small; color: grey; padding: 1em; ">
Redirecting... <a style="color:grey" href="https://URL_Goes_Here">Go to login page</a> if y'all are not automatically redirected.
</Torso>
</HTML> - Navigate to Customize Login Folio in Learn over again. Select Use Custom Page and then upload the updated login JSP file.
- After making the changes, select Preview on the Customize Login Folio to ostend the redirect is working properly.
Users going to the main URL will now be redirected to the login page for the SAML authentication provider. Administrators can however log in using the Learn internal authentication via the default login page: /webapps/login/?action=default_login or/webapps/login/login.jsp).
More than on customizing the login page in the Ultra feel
Source: https://help.blackboard.com/Learn/Administrator/SaaS/Authentication/Implement_Authentication/SAML_Authentication_Provider_Type/Common_Issues_with_SAML_Authentication
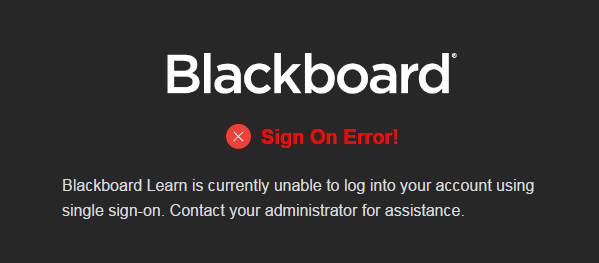
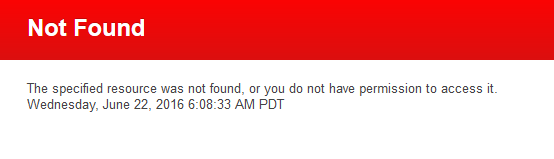
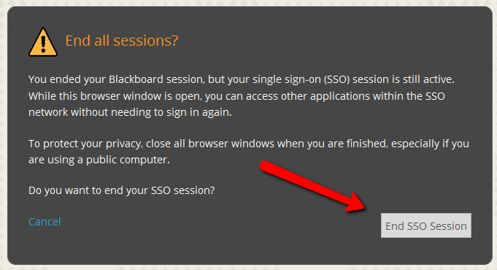

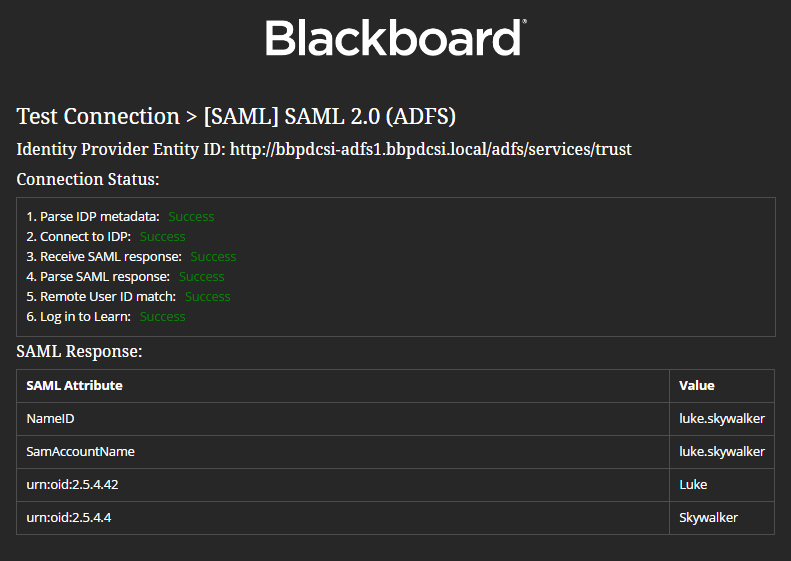
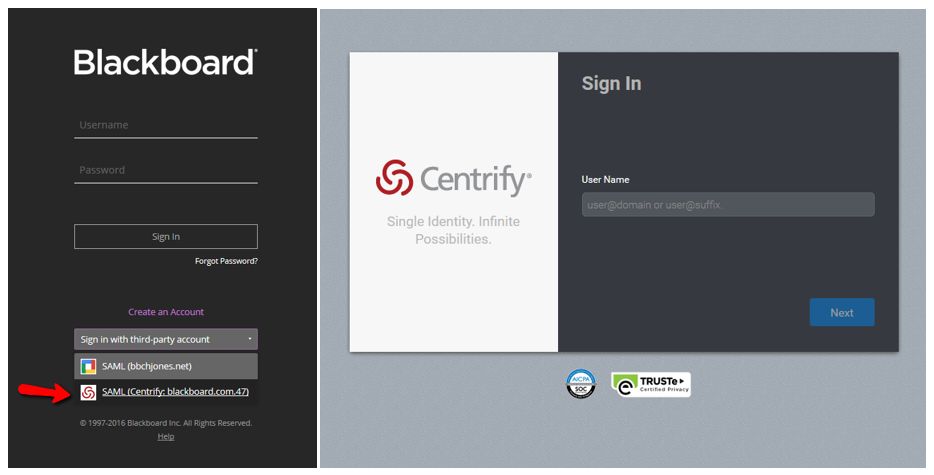
0 Response to "Gtc Blackboard Authentication Failed Try Again"
Postar um comentário